Rogue Access Point Detection Using
Segmental TCP Jitter
Gaogang
XIE Tingting
HE Guangxing
ZHANG
Institute Of
Computing Technology, Institute of Computing
Technology, Institute of Computing Technology,
CAS, 100080
Beijing CAS,
100080ï¼1¤7/span>Beijing CAS,
100080, Beijing
                                       xie@ict.ac.cn hetingting@ict.ac.cn guangxing@ict.ac.cn
-
ABSTRACT
Rogue Access Points (RAPs) pose serious security threats to local networks. An analytic model of prior probability distribution of Segmental TCP Jitter (STJ) is deduced from the mechanism of IEEE 802.11 MAC Distributed Coordinated Function (DCF) and used to differentiate the types of wire and WLAN connections which is the crucial step for RAPs detecting. STJ as the detecting metric can reflect more the characteristic of 802.11 MAC than ACK-Pair since it can eliminate the delay caused by packet transmission. The experiment on an operated network shows the average detection ratio of the algorithm with STJ is more than 92.8% and the average detection time is less than 1s with improvement of 20% and 60% over the detecting approach of ACK-Pair respectively. Farther more no WLAN training trace is needed in the detecting algorithm.
-
Categories and Subject Descriptors
C.2.3[Network Operations]: Network management and monitoring
-
General Terms
Management, Measurement
-
Keywords
Rogue AP, Segmental TCP Jitter, Analytic Model, Sequential Hypothesis Testing.
-
INTRODUCTION
802.11-based wireless access network has been deployed widely recent years due to its unlicensed spectrum, cheap wireless interfaces, high bandwidth and the inherent convenience of computing. However, the vulnerabilities for example DOS attack, wiretapping and incursion have gone all along with and threaten the popularization of WLAN. Rogue Access Point (RAP) is one of the most popular threats [1][2]. The RAP detecting methodologies can be classified into two categories: the Over-the-Air (OTA) and the Over-the-Wire (OTW). OTW has attracted great research force due to its advantages over OTA. MAC/IP address filtering and flow characteristics are two common criterions used in RAP detection [1][2][3]. The methodology based on MAC/IP address filtering will be invalid in the scenes of network address transfer and address spoofing. The flow-based detecting approaches identify the connection categories from the prior possibility distribution of flow characteristics obtained in advance from captured WLAN trace. Unfortunately, usually it is impossible to get these trace for organizations without WLAN.An analytic model of STJ has been deduced from the mechanism of 802.11 MAC DCF and used as the metric to differentiate the link types in this paper. An algorithm of detecting RAPs is proposed based on the analytic model. The experiment result on an operated network shows its advantage over the approaches based on ACK-Pair.
-
RELATED WORK
OTA-based detection approaches parses SSID and MAC of
AP from captured data frames to detect RAPs. Almost all existed detection
instruments provided by vendors used OTA, for example AirDefense, AirMagnet and
AirWave. OTA is generally ineffective because of time-consuming manual scans,
signal range and expensive besides MAC/IP address spoofing. OTW-based detection
approaches determine RAPs using MAC/IP or traffic flow characteristics. Cisco
offers some tools to detect RAPs by querying routers or switches for MAC/IP
address assignment. However, it is of no effect on address spoofing and NAT.
The
main idea of the flow characteristics-based detection methodologies identify
RAPs using binary decision diagram based on the prior probability distribution
of the wire and wireless flows from measurement experiments. The methodologies
can be classified into active and passive measurement according the approach of
obtaining flow characteristics [1][2][3][4]. TCP
Ack-pairs and Inter-packet spacing are two primary properties to detect RAPs.
Ack-pairs based approaches can throw off the disadvantage of MAC/IP based
approaches, but they also require some restriction conditions e.g. the packet
size of TCP should be larger than 1000 bytes, the interval of two sequent
packets should be less than 0.24ms, and all hosts must implement the
mechanism of Delayed ACK.
- ANALYTIC MODEL OF STJ
Let's discuss a TCP connection with WLAN
destination host H. The STJ denoted as j is defined as the RTT
jitter from the detecting site to H. Obviously, j is composed by
jitters in wire (jl) and wireless link (jw).
jw is determined by queuing delay
caused by 802.11 MAC DCF. Signal strength, handover and traffic let jw
increase and different with the characteristic of wire's jitters.
A packet trace
about 8GB is captured from the access link of a campus Intranet with 1500
users. There are 5,121,419 TCP connections from 847 Ethernet and
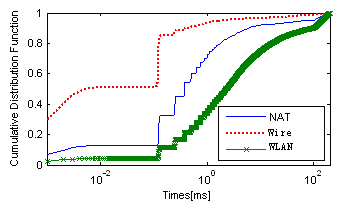
213,163 TCP connections from 57 WLAN users respectively. Their STJs are shown
as Figure 1. From Figure 1, the distribution characteristic of STJ in WLAN is
evidently distinguished from that of Ethernet access.Denoted packet i
queuing delay on AP and wireless host as qA[i] and qs[i],
then
jw[n]=
qA[n]+qS[n]- qA[n-1]-qS[n-1]
(1)
The probability distribution of STJs caused by wireless access can be
deduced from the DCF Markov chain model ignoring the effect of cross traffic as
formula (2).
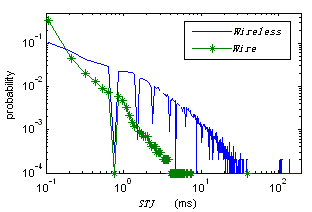
Figure
1. STJs of Ethernet and WLAN Access
![]() (2)
(2)
The
comparing result of cumulative distribution function (CDF) of STJ from the
trace and formula (2) is shown in Figure 2.
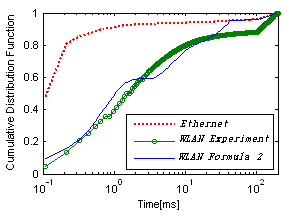
Figure 2. CDF of Theoretical and Experimental WLAN